Mitre ATT&CK Framework Explained
The Mitre Attack Framework was developed by the Mitre corporation in 2013. The tool, called ATT&CK (Advisorial Tactics, Techniques and Common Knowledge) visually represents a cybersecurity attacker’s steps in the arch of a successful breach. The tool was developed to help cybersecurity aspirants and professionals alike better understand the environment where and how breaches occur with respect to the Cyber Kill Chain as define by Lockheed Martin.
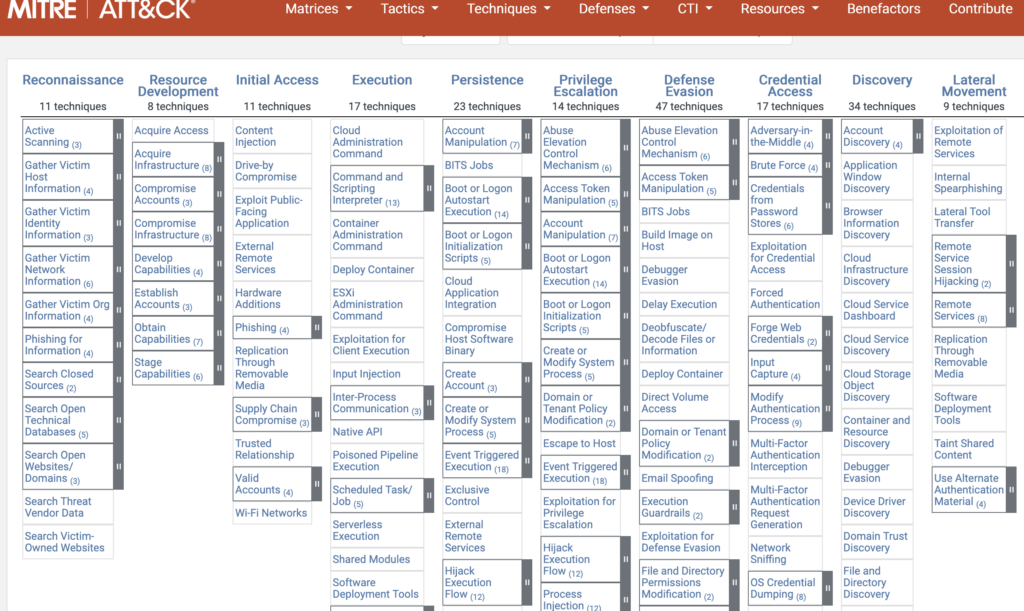
As stated, it’s a visual attack representation that allows the user to interact with the framework as they learn about the techniques and tactics employed by the attackers. At first glance, the ATT&CK framework can be intimidating with its multiple columns and blocks. However, investing a bit of time in understanding the layout and flow will reveal the power and value of the framework; ultimately enhancing the user’s cybersecurity understanding and skills.
The framework consists of these 14 categories:
- Reconnaissance
- Resource Development
- Initial Access
- Execution
- Persistence
- Privilege Escalation
- Defense Evasion
- Credential Access
- Discovery
- Lateral Movement
- Collection
- Command and Control
- Exfiltration
- Impact
The categories (columns) ,defined from left to right, trace the path an attacker takes in their target objectives. For example, reconnaissance is a fundamental first step in understanding the target’s environment and its weaknesses. Resource Development are the actions taken in gathering the necessary tools used to exploit the target’s weaknesses..and so it goes down the line. The execution category delineates the attack between pre-breach and post-breach. As you can see there are many other categories that follow execution, which are the processes taken by the attacker to elevate privileges, evade detection, and employ other similar tactics to maximize the returns of the attack. In some instances, a system is compromised in order to use it to attack a different and possibly the real target. In such a case, evading detection is paramount.
Each category consists of multiple blocks called sub-techniques in that family. These sub-techniques focus on a specific actions that are well researched and documented. A click on a sub-technique directs the user to a page with a wealth of information on that specific technique, tactic, mitigation and detection strategies. For example, the Cloud Administration Command under the Execution category lists the following information:
- Examples of tools and techniques used to exploit AWS and Azure services.
- Mitigation steps to lower their risk.
- Detection strategies that can be used in AWS and Azure.
This granular design and approach makes it easy to drill down on those areas that are relavent to the user’s environment all while remaining within a cybersecurity domain. The well researched, organized and up-to-date content make for a formidable training tool for both defenders and attackers.
The ATT&CK framework is actively maintained, with version 19 on the cusp of release as of this posting. It is a resource rich tool that should be in every cybersecurity professional’s tool bag, or studied at length by those aspiring to enter this field. As for the layperson, this is a great tool for a post-breach (lessons learned) analysis and reporting tool that can help describe the attack in cybersecurity terms and actions used by professionals.
I hope you found this article informative, thought-provoking, or somewhat interesting. I strive to produce content that imparts the most value to those in the IT trenches. I’m happy to hear if you have a different take or additional information that could benefit others.
Best of luck, and feel free to suggest other topics you would like me to address.
Abel Sanchez (abel@staidworks.com) – BankSafeTech Contributor and Moderator


