Categorization and Segmentation
All things and practices that constitute cyber security are vast and deep, often leaving one overwhelmed and dismayed. And the ever-changing nature of technology adds to this malaise. But when all feels lost, there are concepts and age old truths that help you see through the chaos to help deliver and maintain a secure IT environment. In this article, I’ll cover two symbiotic concepts that reduce the complexity of cyber security and strengthen the foundation of any IT environment.
First, the truth: simple designs create strong foundations. The antithesis: complexity is cyber security’s enemy.
In pursuit of a simple design, we start with data categorization. If you think about it, not all data possesses the same level of sensitivity. Your phone number does not need to be safeguarded with the same controls as your social security number or password. The same is true for an organization’s data; there exists a spectrum where at one end we find public data meant for public consumption, and at the other end we find sensitive information such as intellectual property, source code, secret recipe, or financial documents whose access and availability must be restricted. It’s incorrect and inefficient to protect all the data at the same level, either all openly available or all tightly under wraps. A better approach is to categorize data using a few simple, easy to understand categories, and then apply the appropriate level of security to those categories. This is not a novel idea; the Department of Defense (DoD) has been using this very strategy for decades to manage all its information. In general, their categories are public, controlled unclassified data (CUI), secret, and top secret. Each category comes with its own policies and procedures commensurate with their sensitivity and protection requirements. DoD staff are trained on the proper handling, processing and storing of these types of data. In addition, access is issued to personnel with the appropriate need to know. In general, adopting data categories helps the organization properly prioritize resources, scoping, and expenditures required by the data, which includes systems/technologies that secure the data. Does your organization need to have as many categories as the DoD? No. You need at least two: public / private. However, 3 is a better solution: public, internal use, and sensitive, with sensitive being the most secure and most restricted.
This general categorization explanation should be sufficient to give you something to build on. So, how do you implement such a program? For data categories to work, the institution needs to do this:
- Create the data categories and definitions for their purpose.
- Establish a process for categorizing and re-categorizing data.
- Establish a process for marking documents, especially the most sensitive (more on this later)
- Establish policies and procedures for the proper handling, processing, and transmitting of the different types of categories.
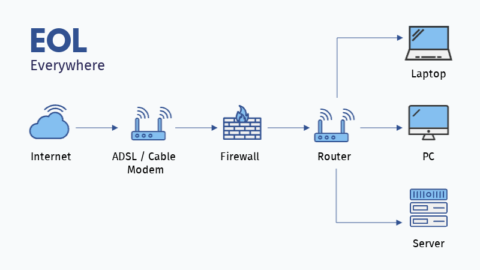
Data categorization is the policy side in the symbiotic concepts introduced here; segmentation is the application of the policy. Segmentation of networks and data is a key practice in robust cybersecurity. The idea of segmentation, or rather the physical and/or virtual separation of information systems and data based on importance and sensitivity, provides a sound framework for organizing and securing data for improved risk management.
Segmentation is driven by data categorization; separate and enforce security protections based on the sensitivity of the data. The strength of IT segmentation can be visualized using a shopping mall metaphor; when the mall is closed, all the shops in the mall have their own security gates pulled down and locked. Should someone break into the mall, they would still need to break into the shop. This additional layer of security imparts multiple benefits:
- Delays and or thwarts the attack.
- Opportunities to trigger incident response mechanisms during the first-layer attack.
- Limits the scope of damage. (Not all areas suffer the same impact)
- Infinitely recursive (segmentation within segmentation within segmentation, etc.)
Even a simple 3 category (public, internal use, sensitive) approach makes it easier to identify where the organization should invest cyber security time and effort. Public websites and customer-provided WIFI do not require a lot of security other than standard patches and updates, which is true for any system on the network regardless of sensitivity. The data and their systems should operate outside or aside of the organization’s network, and are deemed ‘expendable’ in the greater data protection battle.
Data categorized as ‘Internal Use’, typically business operations, makes up the majority of what needs to be secured and what businesses expend most of their cyber security dollars on. Internal use data is secured with firewalls, access and identity management systems, threat identification technologies, encryption, and business continuity and disaster recovery programs, to name a few.
The final category is ‘sensitive’. Depending on the level of sensitivity, the data may or may not reside inside the business’ internal use network. There may be a reason why this information should be encrypted and stored in a separate (non-business-affiliated) network. There may be a reason to restrict who and how the data is accessed. To be sure, cyber security safeguards still apply, regardless of their ‘secret’ location, but the point is to shrink the pool of those with the need to know and the means to retrieve the information.
I mentioned document marking in the list of requirements above, and it’s key for the proper safeguarding of sensitive information. What do markings accomplish?
- Makes clear that the information is sensitive (based on the category definition) to the holder of the data and their responsibilities to protect it. An unmarked document looks like any other and thus may fail to get the proper security applied.
- The marking conveys to the holder established policies, procedures, and protocols for the proper security, dissemination, and disposal of its content.
- Triggers an incident response when the content is found in a non-compliant environment.
Consistent document markings have always been challenging even for the most deft and fastidious types, so it’s not something that is easily maintained. Perhaps applying document markings to the most sensitive category is the most pragmatic, achievable, and sustainable in the grand scheme.
Hopefully, its evident by now how categorizing and segmenting information systems leads to a clearer field of vision by breaking down a complex problem into small pieces. This de-muddles security complexity and simplifies the task of applying cyber security controls in a logical and measured stratagem.
I hope you found this article informative, thought-provoking, or somewhat interesting. I strive to produce content that imparts the most value to those in the IT trenches. I’m happy to hear if you have a different take or additional information that could benefit others.
Best of luck, and feel free to suggest other topics you would like me to address.
Abel Sanchez (abel@staidworks.com) – BankSafeTech Contributor and Moderator